Introduction to Research Practices
Published:
As part of ENGG1600: Introduction to Research Practices through the duration of a semester I conducted research to determine the effectiveness of various machine learning algorithms to detect network intrusions and the beginning of DDoS attacks. The aim of this research was to test algorithms presented in existing papers to determine whether further investigation should be done.
I found this to be an extremely difficult task since I had only learnt the basics of programming the semester prior to this. I am thankful for all the help I got from my Research Supervisor Abigail Koay and Research Partner Benjamin Tran.
This course consisted of three major pieces of assessment noted blow. A critical review of existing literature, a research paper under the supervision of an academic, and a presentation of the research findings.
Critical Review
Our first assessment task was to review an existing piece of literature with our supervisor’s approval around the research topic given. While I was investigating potential algorithms to test, the one I wrote about stood out due to how well the authors hid their implementation’s inefficiency. The critical review can be found here: Critical Review of Semi-Supervised K-Means DDoS Detection Method Using Hybrid Feature Selection Algorithm.
Research Paper
My final paper was a summation of the literature I had read previously and how the results presented matched the testing conducted over the twelve-week period. The conclusion of my paper was that more transparency and standardisation is needed for Machine Learning research. Reproducibility can be incredibly difficult due to a lack of transparency of algorithms have been modified, data has been pruned, what systems were used to test, and what results papers present. The full paper is: Efficiency of Machine Learning Methods in the Detection of DDoS Attacks.
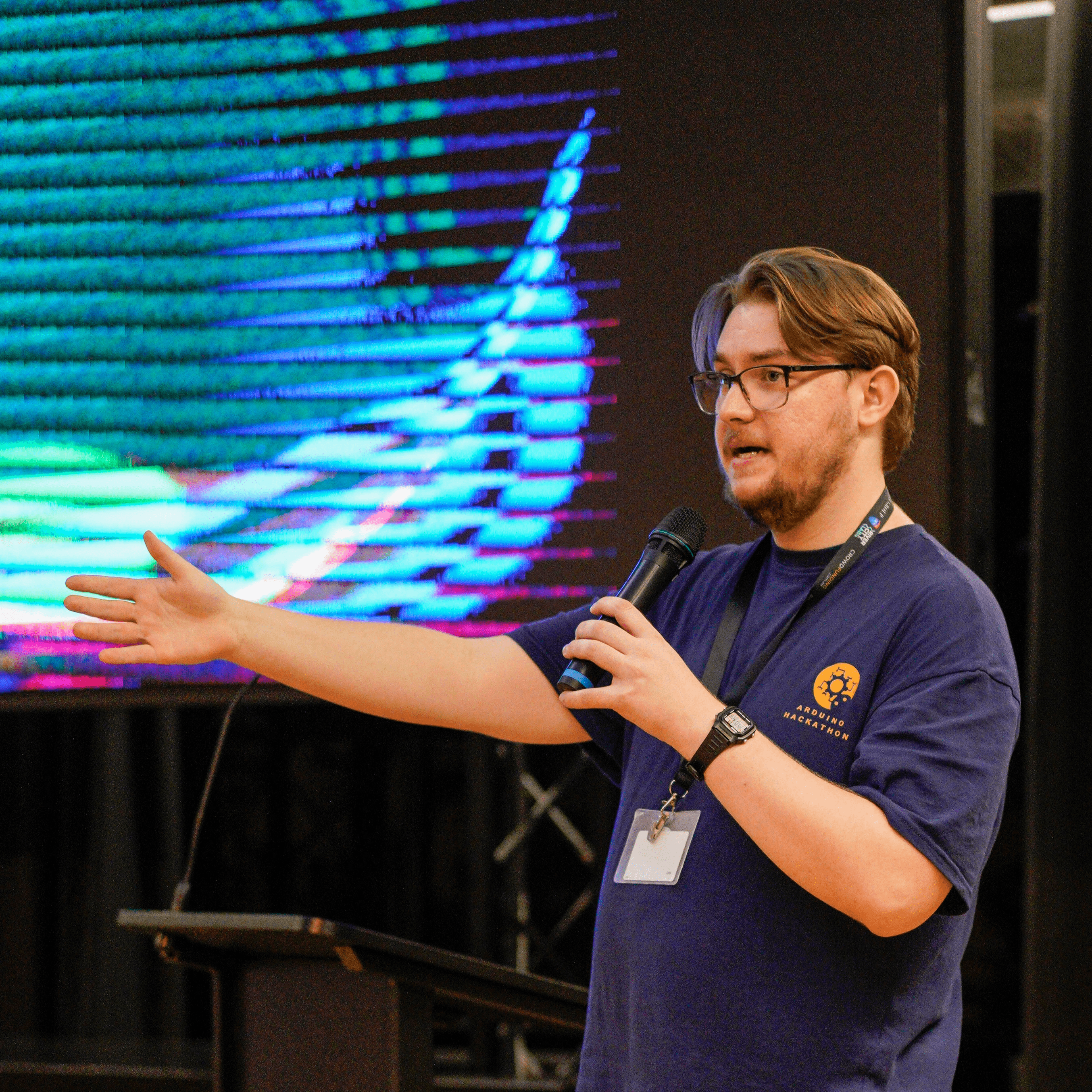
Presentation
At the end of the course, we each presented what we had been working on during the semester and our findings. It was great to see all the amazing projects that others had been working on in full detail. My presentation can be found here: Extending Entropy Beyond DDOS Detection